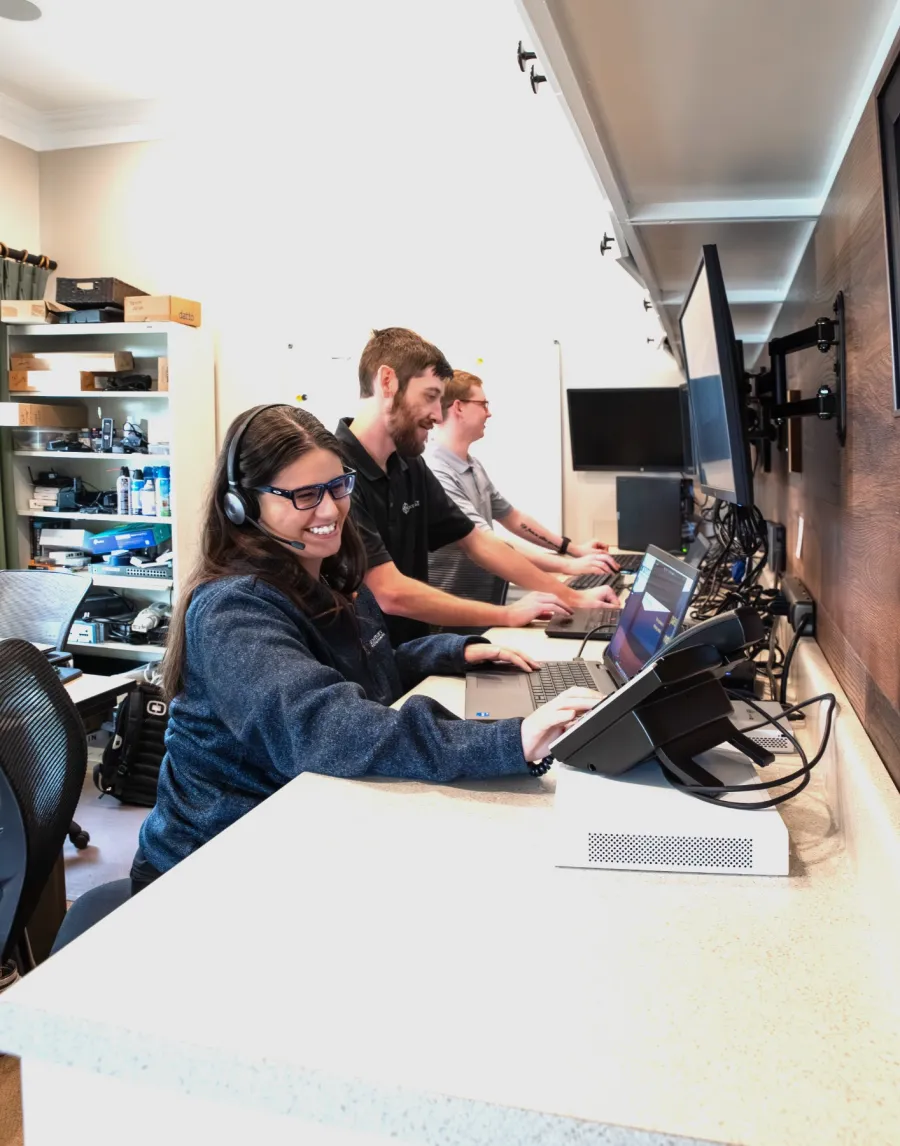
Upgrade Your Business with Responsive Support
And Reliable IT
Discover Best In Lexington IT Support That's Been Offering Secure Technology Solutions Since 2001, Letting You Concentrate On Success

Don’t Let Poor IT Support Drag Your Business Down
Unreliable IT services can do more than just slow you down—they can jeopardize your entire business. At Next Century Technologies, we understand that slow response times, outdated technology, and constant technical issues can lead to severe consequences. Here's what you risk if you don't take action:
Disruption in your daily operations due to frequent technical glitches
Prolonged downtime impacting your productivity and revenue
Increased vulnerability to cyber threats and data breaches
Frustration and stress from slow responses and unresolved issues
Potential regulatory non-compliance, leading to fines and legal issues
Loss of customer trust and damaged reputation
Unmatched Benefits Of Next Century Technologies IT Support And Services
We guarantee to respond to your IT issues swiftly, minimizing downtime and keeping your business running smoothly. Our team is available 24/7, ensuring that you never have to wait days for support.
Expert Compliance and Security
Our expertise includes HIPAA, FTC safeguards, financial compliance, and cybersecurity, providing you peace of mind that your business is protected against regulatory breaches and cyber threats.
Proactive IT Management
We don't just fix problems; we prevent them. Our proactive approach means fewer technical issues and more efficient operations, so you can focus on your core business.
Dedicated Account Management
Our personalized approach means you have a dedicated team that understands your unique needs. This ensures consistent, reliable service tailored to your business goals.
Reliable Local Support
With over 23 years in business and numerous local clients, we are a trusted IT partner in the Lexington area. Our commitment to excellent customer service has earned us the Best in Lex award.
Next Century Technologies: Trusted IT Partner Serving Lexington Businesses for Over 23 Years
We understand how overwhelming it can be to deal with constant technical issues and system downtimes. At Next Century Technologies, we pride ourselves on being a reliable IT partner for your business. With over 23 years in the industry, we have established a reputation for providing responsive, knowledgeable, and consistent IT support - winning us Best in Lex for outstanding customer service and IT solutions.
Our clients appreciate our commitment to solving their IT challenges swiftly and efficiently. We recognize that frequent technical problems and slow response times can leave you feeling stressed and taken advantage of. That's why our low employee turnover and 24/7 availability ensures that you work with the same dedicated team who knows your business inside and out. We bring practical solutions to your IT issues, allowing you to focus on growing your business without the burden of technical disruptions, and we offer a 90-day satisfaction guarantee to ensure we're the right IT partner for your business.
Here's What Our Clients Are Saying About Our Services
At Next Century Technologies, We Simplify Your IT Experience
At Next Century Technologies we know that you want to be successful in business, both to your peers and your family. To achieve that, you need dependable IT services that keep your operations running smoothly.
The problem is that frequent technical glitches and slow responses from your current IT provider make you feel angry, stressed and overwhelmed. We believe that technology should empower your business, not hold it back.
We empathize with the frustration of dealing with unreliable IT support. That's why we offer comprehensive, responsive IT solutions backed by over 23 years of industry experience and a dedicated, knowledgeable team.