
As a veterinary professional in Kentucky, your priority is providing quality care to animals—but there's another vital responsibility you carry: safeguarding patient medical records. Under Kentucky law,...

If I asked you to identify the most significant cybersecurity threats in your office, you might mention phishing emails, malware, or weak passwords. However, what if I told you that your office printer, the one...

A client recently asked me about the common mistakes business owners make regarding IT and cybersecurity. Where to start… After years of experience with businesses of all sizes, the most significant mistake...

Chatbots such as ChatGPT, Gemini, Microsoft Copilot, and the newly launched DeepSeek have transformed our interactions with technology, assisting with a wide range of tasks from composing emails and generating...
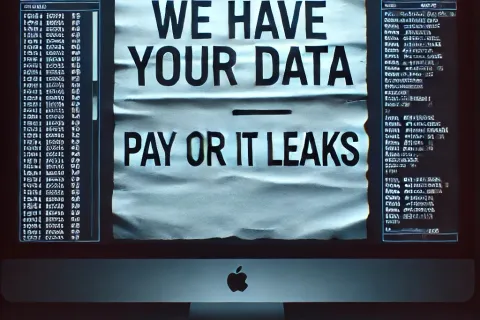
Think ransomware is your worst nightmare? Think again. Hackers have discovered a new method to hold your business hostage, and it could be even more ruthless than traditional encryption. This tactic, known as data...

Mark your calendars: October 14, 2025 - the date when Windows 10 officially reaches its end of life. After this date, Microsoft will cease to provide security updates, bug fixes, or technical support for Windows 10....

When it comes to running a business, most owners focus on factors like quality customer service, dependable products or services, and closely monitored profit and loss statements as key indicators of success or...

Business e-mail compromise (BEC) is rapidly emerging as one of the most significant cyber threats that businesses encounter. While these scams have posed challenges for organizations for years, the advent of advanced...
Imagine you and your team arrive at work, ready to tackle the day's tasks, when suddenly the Internet goes down. Emails stop working, and productivity comes to a standstill. What would you do? For many businesses, an...